Key considerations and solutions to ensure cyber resiliency in the smart integrated energy systems
The document contains an overview of the subject, identifies, and categorizes the types of cyberattacks on the exposed energy system components and their possible consequences, and concludes with a set of managerial- and technical-level measures and policy recommendations to mitigate the cybersecurity risks
4 Types of Cyber-Attacks on the Smart Grid That Can Endanger Energy Security
The document contains an overview of the subject, identifies, and categorizes the types of cyberattacks on the exposed energy system components and their possible consequences, and concludes with a set of managerial- and technical-level measures and policy recommendations to mitigate the cybersecurity risks
Data storage and destruction. Here's how it works
Data storage on computers, phones, even smart home devices. They all have a hard drive, also known as a hard disk, to store data. It's so obvious that we probably don't think about it, just as we hardly think about what our brains store in everyday life. But however inconspicuous it may be, we can't do without it. And, good news, removing information from a hard drive is much easier than from our memory. This article explains how this works.
A social engineering test - How does that work? | Introduction into the methodology of a penetration test, part 7
Previous articles have already looked at the methodology for 1) web application, 2) perimeter, 3) hardware, 4) mobile app, 5) WLAN, and 6) local network testing. As the conclusion to the series “Introduction to the methodology of a penetration test,” this article provides an insight into the “social engineering” testing method.
An internal network test - How does that work? | Introduction into the methodology of a penetration test, part 6
Previous articles have already looked at the methodology for 1) web application, 2) perimeter, 3) hardware, 4) mobile app, and 5) Wi-Fi testing. This article now provides an introduction to performing an internal network test.
A wifi test - How does that work? | Introduction into the methodology of a penetration test, part 5
Previous articles have already looked at the methodology for 1) web application, 2) perimeter, 3) hardware, and 4) mobile app testing. This article provides an introduction to performing a Wi-Fi test.
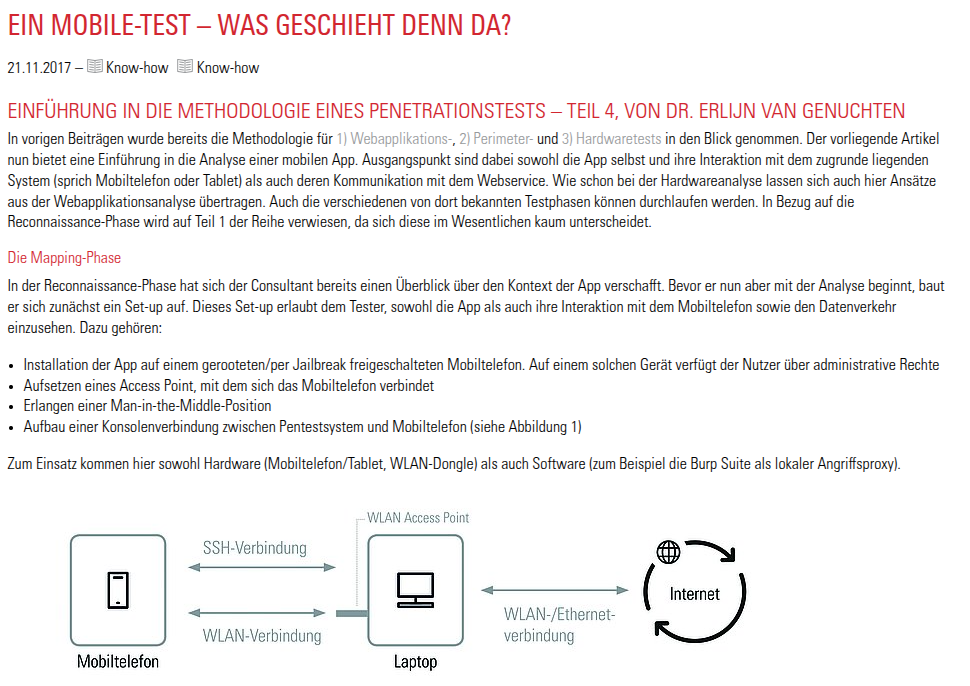
A mobile test - How does that work? | Introduction into the methodology of a penetration test, part 4
Previous articles have already looked at the methodology for 1) web application, 2) perimeter, and 3) hardware testing. This article now offers an introduction to the analysis of a mobile app.
A hardware test - How does that work? | Introduction into the methodology of a penetration test, part 3
Since SySS Newsletter 3/2015, we have been regularly discussing the “Introduction to the Methodology of a Penetration Test” in this blog. Starting with the procedure for web application testing, this was followed in December 2016 by a description of how to perform a perimeter test. This article continues the series and focuses on hardware analysis.
The invisible
The main goal of a penetration test is to uncover vulnerabilities. Analyzing the visible attack surface plays a crucial role in this process. If we compare a digital attacker to a burglar, we could say that even a thief needs to be able to see the front door of a house in order to pick the lock. But “the visible” is often only the tip of the iceberg in IT security. This article explains why.
Where is the S in IoT? About IT-security in the Internet of Things
IT security has reached a new dimension in the field of IoT. More and more poorly secured or completely unsecured Internet-enabled devices are becoming accessible worldwide—an open door for attackers. Developers of IoT products should therefore familiarize themselves with existing measures that can be used to mitigate potential risks.
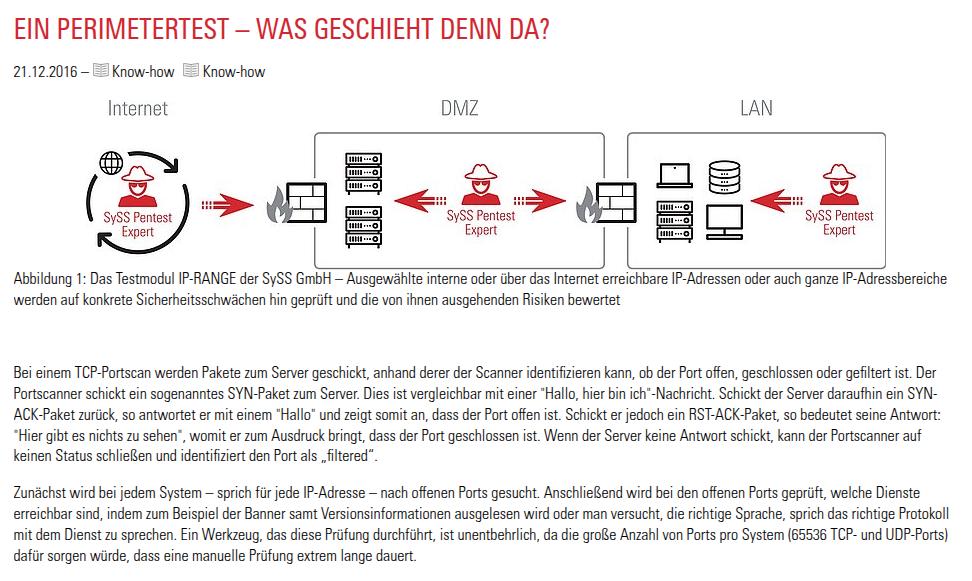
A perimeter test - How does that work? | Introduction into the methodology of a penetration test, part 2
During a TCP port scan, packets are sent to the server, which the scanner uses to identify whether the port is open, closed, or filtered, providing information which services are available. This article explains how a perimeter test works
A web application test - How does that work? | Introduction into the methodology of a penetration test
To give customers and those interested in IT security an insight into the procedure for a security analysis, the following section describes how a web application test is carried out.